The Identity Platform Built on Passwordless-First Principles
Trustaige doesn't bolt passwordless onto a legacy architecture. Every capability — access control, provisioning, compliance, threat detection — is built on a foundation of cryptographic proof, not shared secrets.
From Shared Secrets to Cryptographic Proof
Every password-based system relies on the same fragile premise: both the user and the server know the secret. Trustaige operates on a fundamentally different model.
When a user enrolls, their device generates a cryptographic key pair. The private key is locked inside the device's secure hardware — it never leaves. The public key is sent to the server. It's useless on its own.
This is not an incremental improvement to passwords. This is the foundation every other capability is built on.
User Enrolls
Device generates a key pair. Private key stays in secure hardware.
Public Key Stored
Server stores the public key. It can verify, but never produce, a signature.
Biometric Verification
User's biometric unlocks the private key. Device signs the challenge.
Identity Proven
No password crosses the network. No secret stored on the server.
Built for the Way Security Teams Actually Work
Every screen is designed for clarity — from the analytics overview to individual audit events.
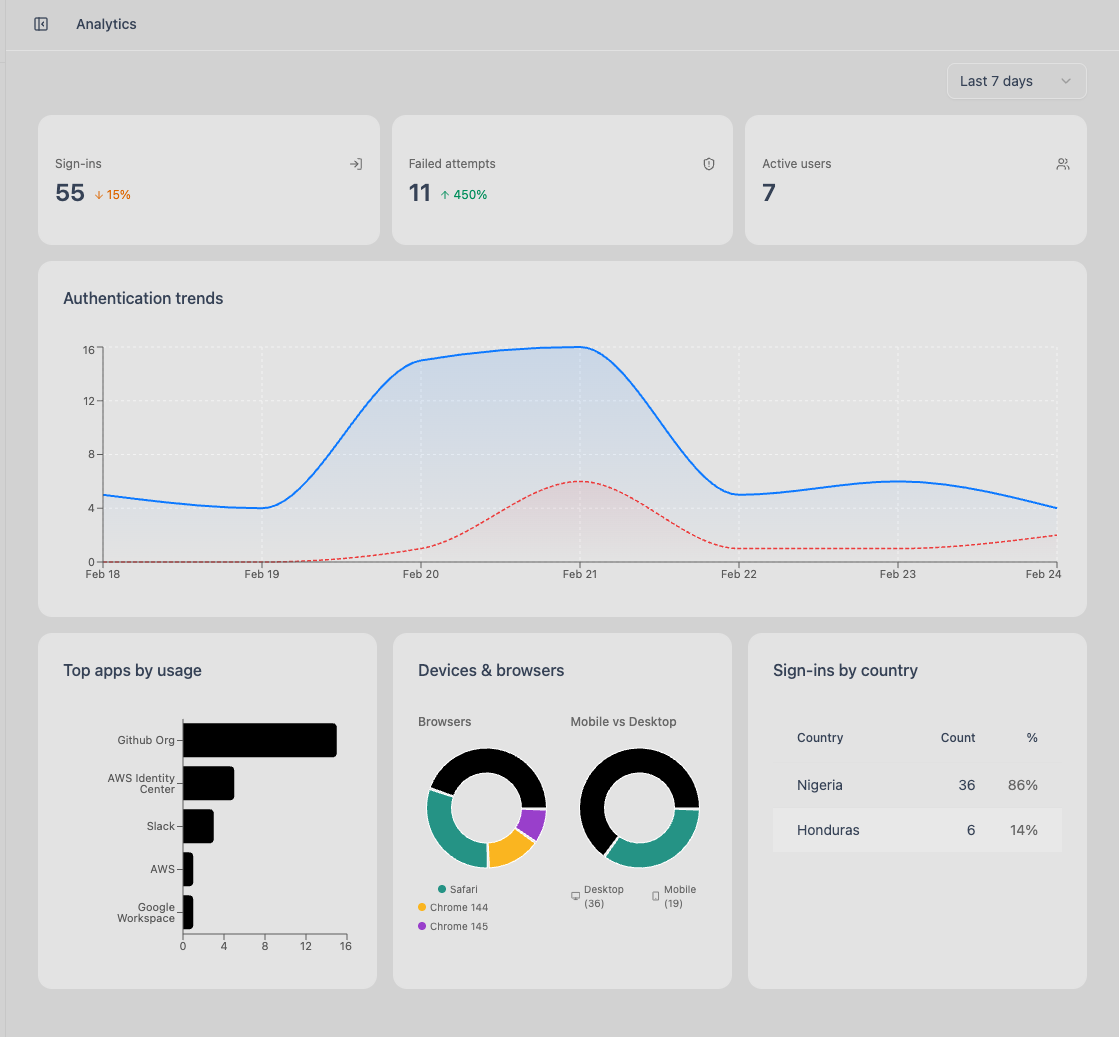
Analytics dashboard — authentication trends, device usage, and geographic distribution
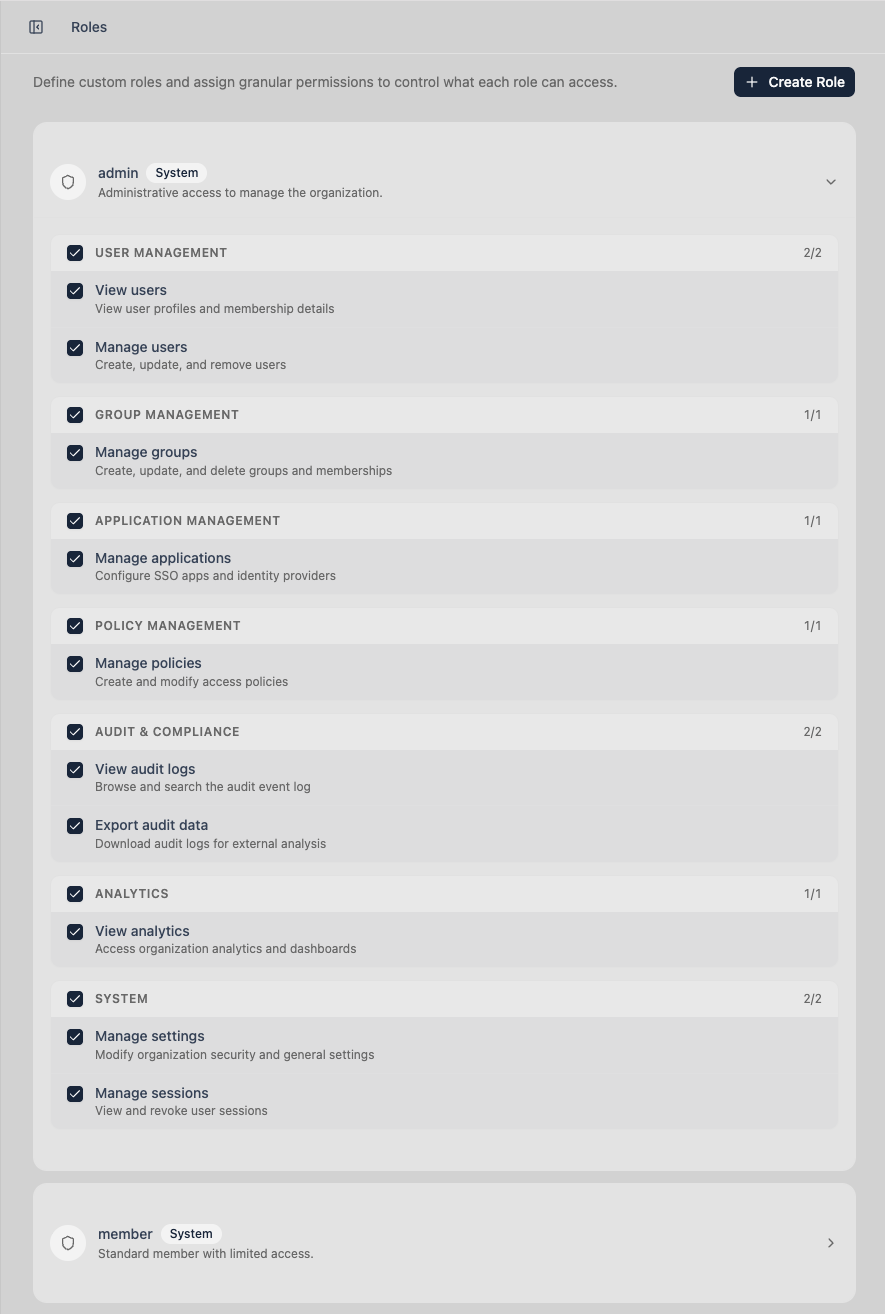
Role-based access control with granular permissions
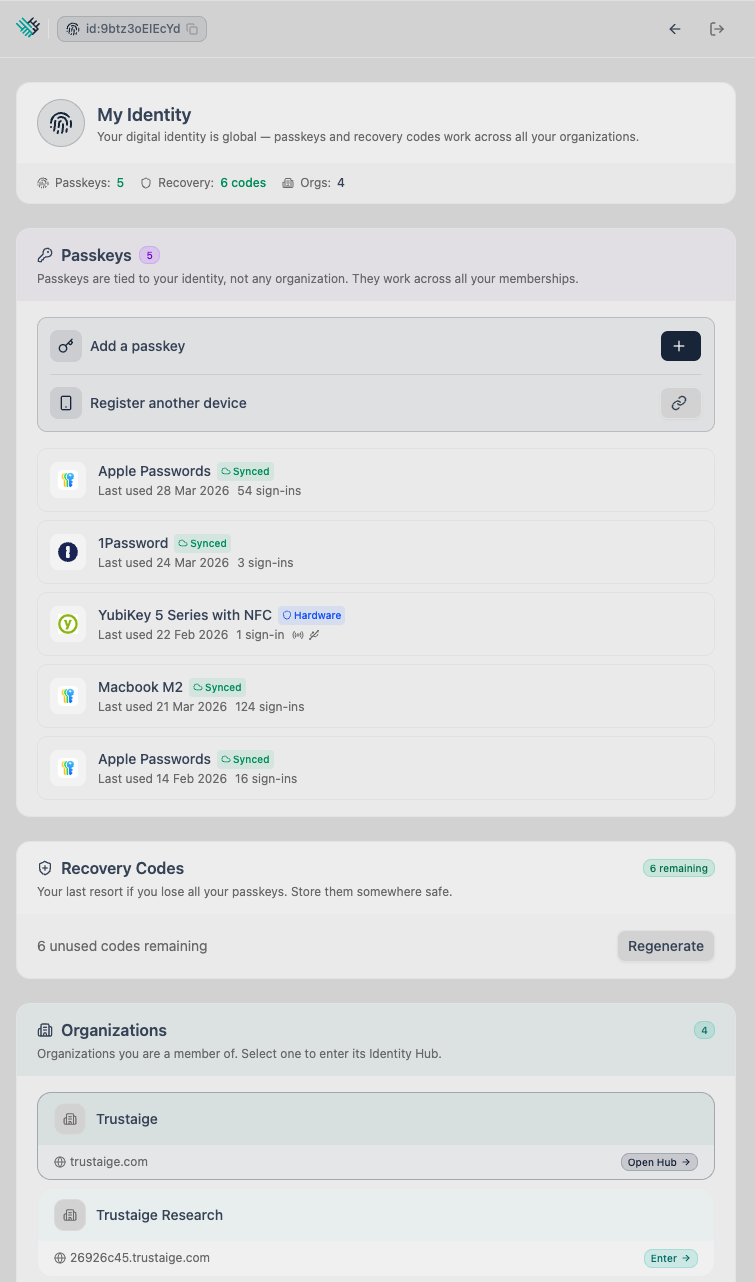
Passkey management with device and authenticator details
The Cost of the Password Layer
Analyst time, employee downtime, and process overhead for every single reset event.
The shared secret model is fundamentally broken. Complexity policies cannot fix an architectural failure.
No passwords to steal. No OTPs to intercept. Cryptographic proof replaces shared secrets.
Everything You Need to Run Enterprise Identity
Six capability areas — each built on the same passwordless-first foundation. No passwords to manage, no shared secrets to protect, no legacy workarounds.
Access Management
Control who can access which applications based on team structure, role, and custom policies — enforced automatically. Groups, dynamic membership, access policies, and role-based admin control.
Explore Access ManagementLifecycle & Provisioning
Automate the entire user journey — from first-day onboarding to same-day offboarding — across every connected application. SCIM sync, bulk import, and device enrollment.
Explore ProvisioningVisibility & Analytics
See authentication activity, device health, and access patterns across your organization in real time.
Learn moreThreat Detection & Response
Detect new devices, impossible travel, and anomalous sessions — and respond before damage is done.
Learn moreCompliance & Governance
Exportable audit trails, credential compliance reporting, and configurable security policies for your regulatory requirements.
Learn moreIntegration & Automation
Connect your stack with webhooks, pre-built app templates, and a full Admin API. Standards-based protocols throughout.
Learn moreBuilt on Open Standards
No proprietary lock-in. Built on interoperable standards maintained by the organizations that govern the web.
Ready to Replace Your Password Layer?
Start a 30-day free trial. Set up passwordless authentication for your team in minutes. No credit card required.