Threat Detection & Response
Automatically detect suspicious access patterns — new devices, impossible travel, anomalous sessions — and respond before damage is done.
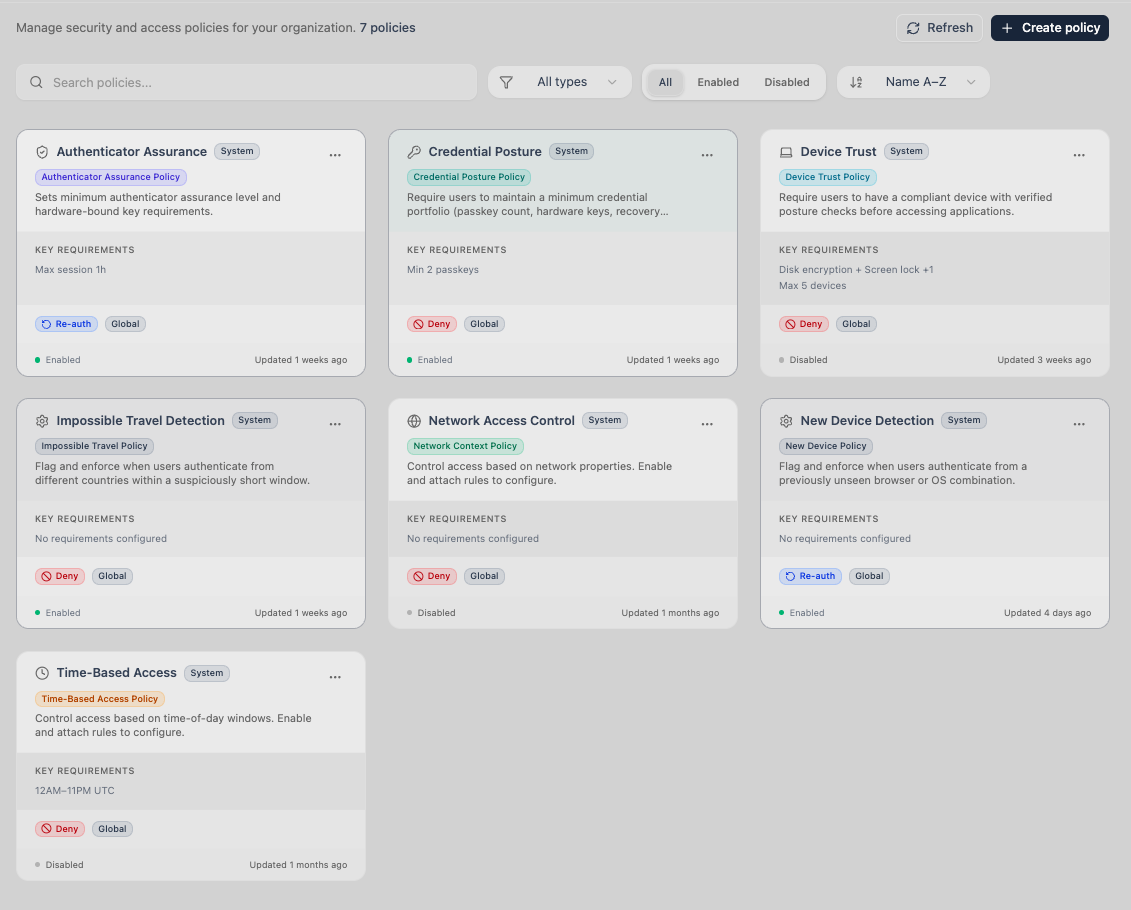
Key Features
New Device Detection
When a user authenticates from a device that hasn't been seen before, Trustaige flags it immediately. Pair with access policies to require additional verification or block access until an admin approves.
Impossible Travel Detection
If a user logs in from Lagos and then from London twenty minutes later, something is wrong. Geographic analysis identifies physically impossible access patterns and triggers policy enforcement.
Session Control
Configure session duration and idle timeouts per organization. View all active sessions with device and location details. Revoke individual sessions or terminate all sessions for a user with one action.
Identity Recovery
When a user loses access to their device, one-time recovery codes allow secure re-enrollment without IT intervention. Recovery triggers device registration — the user proves their identity and enrolls a new passkey.
Why This Is Better Without Passwords
Password-based threat detection is overwhelmed by noise — credential stuffing, password spraying, brute force attempts. Security teams spend their time sifting through millions of failed login events that wouldn't exist without passwords. Trustaige eliminates that entire attack surface. Threat detection focuses on what matters: behavioral anomalies like new devices, unusual locations, and impossible travel patterns.
Explore Related Capabilities
Ready to Replace Your Password Layer?
Start a 30-day free trial. Set up passwordless authentication for your team in minutes. No credit card required.